Generate Gpg Key Pair Error
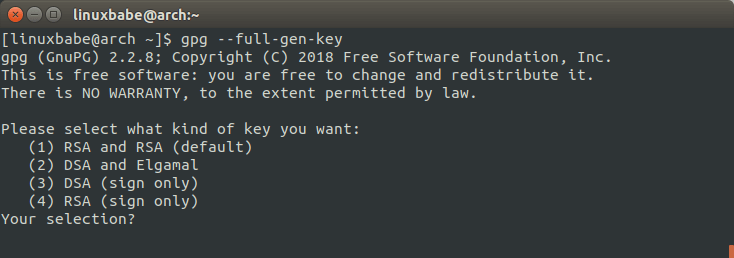
After building your custom RPM package, it's a good idea to sign the package with your own GPG Key to make sure the package is authentic. In this HOWTO, I'll cover how to generate your own gpg key pair and sign your custom RPM package with that key. First create a hidden directory called '.gnupg. If you are on version 2.1.17 or greater, paste the text below to generate a GPG key pair. $ gpg -full-generate-key; If you are not on version 2.1.17 or greater, the gpg -full-generate-key command doesn't work. Paste the text below and skip to step 6. $ gpg -default-new-key-algo rsa4096 -gen-key.
- Table of Contents
- Generating a new keypair
- Exchanging keys
- Encrypting and decrypting documents
- Making and verifying signatures
Jul 01, 2019 Once GnuPG is installed, you’ll need to generate your own GPG key pair, consisting of a private and public key. The private key is your master key. It allows you to decrypt/encrypt your files and create signatures which are signed with your private key. It is likely that you are running out of entropy. Key generation requires a lot of very high-quality random numbers; without the activity of the user to provide high-quality randomness to the computer, the entropy pool is being exhausted by generation, and the generation process just hangs, waiting for the pool to refill. Jun 30, 2018 GPG will generate your keys. We need to generate a lot of random bytes. It is a good idea to perform some other action (type on the keyboard, move the mouse, utilize the disks) during the prime generation; this gives the random number generator a better chance to gain enough entropy. It will take a while for GPG to generate your keys. While it's not a public need ATM, I'm not going to use the key that was exported to my home directory on the digital ocean vps and instead generate a new one. But just out of curiosity, Say I had a public need for the GPG key sometime down the road, how am I going to look with two keys out on key servers with essentially the same identification? In the first screen, you should accept the default option: (1) DSA and ElGamal. This option allows you to create a digital signature and encrypt (and decrypt) with two types of technologies. Type 1 and then press Enter. Next, choose the key size, or how long the key should be.
GnuPG is a tool for secure communication.This chapter is a quick-start guide that covers the core functionalityof GnuPG.This includes keypair creation, exchanging and verifying keys, encryptingand decrypting documents, and authenticating documents with digitalsignatures.It does not explain in detail the concepts behind public-key cryptography,encryption, and digital signatures.This is covered in Chapter 2.It also does not explain how to use GnuPG wisely.This is covered in Chapters 3 and 4.
GnuPG uses public-key cryptography so that users may communicate securely.In a public-key system, each user has a pair of keys consisting ofa
Driver genius 16 key generator download. You can use Driver Genius Keygen in all kinds of devices including the MAC system that is operating. Driver Genius Pro Crack + License KeyThe program also contains a powerful scan function.
The command-line option
You must also choose a key size.The size of a DSA key must be between 512 and 1024 bits, and an ElGamalkey may be of any size.GnuPG, however, requires that keys be no smaller than 768 bits.Therefore, if Option 1 was chosen and you choose a keysize larger than1024 bits, the ElGamal key will have the requested size, but the DSAkey will be 1024 bits.
Finally, you must choose an expiration date.If Option 1 was chosen, the expiration date will be used for both theElGamal and DSA keypairs.
You must provide a user ID in addition to the key parameters.The user ID is used to associate the key being created with a realperson.
GnuPG needs a passphrase to protect the primary and subordinate private keys that you keep in your possession.
After your keypair is created you should immediately generate a revocationcertificate for the primary public key using the option
Notes
[1]Option 3 is to generate an ElGamal keypair that isnot usable for making signatures.
Next: Signing Keys, Previous: Manipulating Keys, Up: Key Management [Contents][Index]
7.5.5 Generating Keys
GPGME provides a set of functions to create public key pairs. Most ofthese functions require the use of GnuPG 2.1 and later; for olderGnuPG versions the gpgme_op_genkey function can be used.Existing code which wants to update to the new functions or new codewhich shall supports older GnuPG versions may try the new functionsfirst and provide a fallback to the old function if the error codeGPG_ERR_NOT_SUPPORTED is received.
SINCE: 1.7.0
The function gpgme_op_createkey generates a new key for theprocotol active in the context ctx. As of now this functiondoes only work for OpenPGP and requires at least version 2.1.13 ofGnuPG.
userid is commonly the mail address associated with the key.GPGME does not require a specific syntax but if more than a mailaddress is given, RFC-822 style format is suggested. The value isexpected to be in UTF-8 encoding (i.e. no IDN encoding for mailaddresses). This is a required parameter.
algo specifies the algorithm for the new key (actually a keypairof public and private key). For a list of supported algorithms, seethe GnuPG manual. If algo is NULL or the string'default', the key is generated using the default algorithm of theengine. If the string 'future-default' is used the engine may use analgorithm which is planned to be the default in a future release ofthe engine; however existing implementation of the protocol may not beable to already handle such future algorithms. For the OpenPGPprotocol, the specification of a default algorithm, without requestinga non-default usage via flags, triggers the creation of aprimary key plus a secondary key (subkey).
reserved must be set to zero.
expires specifies the expiration time in seconds. If you supply0, a reasonable expiration time is chosen. Use the flagGPGME_CREATE_NOEXPIRE to create keys that do not expire. Notethat this parameter takes an unsigned long value and not atime_t to avoid problems on systems which use a signed 32 bittime_t. Note further that the OpenPGP protocol uses 32 bitvalues for timestamps and thus can only encode dates up to the year2106.
extrakey is currently not used and must be set to NULL.A future version of GPGME may use this parameter to create X.509 keys.
flags can be set to the bit-wise OR of the following flags:
GPGME_CREATE_SIGNGPGME_CREATE_ENCRGPGME_CREATE_CERTGPGME_CREATE_AUTHSINCE: 1.7.0
Do not create the key with the default capabilities (key usage) of therequested algorithm but use those explicitly given by these flags:“signing”, “encryption”, “certification”, or “authentication”.The allowed combinations depend on the algorithm.
If any of these flags are set and a default algorithm has beenselected only one key is created in the case of the OpenPGPprotocol.
GPGME_CREATE_NOPASSWDSINCE: 1.7.0
Request generation of the key without password protection.
GPGME_CREATE_SELFSIGNEDSINCE: 1.7.0
For an X.509 key do not create a CSR but a self-signed certificate.This has not yet been implemented.
GPGME_CREATE_NOSTORESINCE: 1.7.0
Do not store the created key in the local key database.This has not yet been implemented.
GPGME_CREATE_WANTPUBGPGME_CREATE_WANTSECSINCE: 1.7.0
Return the public or secret key as part of the result structure.This has not yet been implemented.
GPGME_CREATE_FORCESINCE: 1.7.0
The engine does not allow the creation of a key with a user IDalready existing in the local key database. This flag can be used tooverride this check.
GPGME_CREATE_NOEXPIRESINCE: 1.8.0
Request generation of keys that do not expire.
After the operation completed successfully, information about thecreated key can be retrieved with gpgme_op_genkey_result.
The function returns zero on success, GPG_ERR_NOT_SUPPORTED ifthe engine does not support the command, or a bunch of other errorcodes.
SINCE: 1.7.0
The function gpgme_op_createkey_start initiates agpgme_op_createkey operation; see there for details. It mustbe completed by calling gpgme_wait on the context.See Waiting For Completion.
SINCE: 1.7.0
The function gpgme_op_createsubkey creates and adds a newsubkey to the primary OpenPGP key given by KEY. The onlyallowed protocol in ctx is GPGME_PROTOCOL_OPENPGP.Subkeys (aka secondary keys) are a concept in the OpenPGP protocol tobind several keys to a primary key. As of now this function requiresat least version 2.1.13 of GnuPG.
key specifies the key to operate on.
algo specifies the algorithm for the new subkey. For a list ofsupported algorithms, see the GnuPG manual. If algo isNULL or the string 'default', the subkey is generated using thedefault algorithm for an encryption subkey of the engine. If thestring 'future-default' is used the engine may use an encryptionalgorithm which is planned to be the default in a future release ofthe engine; however existing implementation of the protocol may not beable to already handle such future algorithms.
reserved must be set to zero.
expires specifies the expiration time in seconds. If you supply0, a reasonable expiration time is chosen. Use the flagGPGME_CREATE_NOEXPIRE to create keys that do not expire. Notethat this parameter takes an unsigned long value and not atime_t to avoid problems on systems which use a signed 32 bittime_t. Note further that the OpenPGP protocol uses 32 bitvalues for timestamps and thus can only encode dates up to the year2106.
flags takes the same values as described above forgpgme_op_createkey.
After the operation completed successfully, information about thecreated key can be retrieved with gpgme_op_genkey_result.
The function returns zero on success, GPG_ERR_NOT_SUPPORTED ifthe engine does not support the command, or a bunch of other errorcodes.
SINCE: 1.7.0
The function gpgme_op_createsubkey_start initiates agpgme_op_createsubkey operation; see there for details. It mustbe completed by calling gpgme_wait on the context.See Waiting For Completion.
SINCE: 1.7.0
The function gpgme_op_adduid adds a new user ID to the OpenPGPkey given by KEY. Adding additional user IDs after key creationis a feature of the OpenPGP protocol and thus the protocol for thecontext ctx must be set to OpenPGP. As of now this functionrequires at least version 2.1.13 of GnuPG.
key specifies the key to operate on.
userid is the user ID to add to the key. A user ID is commonlythe mail address to be associated with the key. GPGME does notrequire a specific syntax but if more than a mail address is given,RFC-822 style format is suggested. The value is expected to be inUTF-8 encoding (i.e. no IDN encoding for mail addresses). This is arequired parameter.
flags are currently not used and must be set to zero.
The function returns zero on success, GPG_ERR_NOT_SUPPORTED ifthe engine does not support the command, or a bunch of other errorcodes.
SINCE: 1.7.0
The function gpgme_op_adduid_start initiates agpgme_op_adduid operation; see there for details. It mustbe completed by calling gpgme_wait on the context.See Waiting For Completion.
SINCE: 1.7.0
The function gpgme_op_revuid revokes a user ID from the OpenPGPkey given by KEY. Revoking user IDs after key creation is afeature of the OpenPGP protocol and thus the protocol for the contextctx must be set to OpenPGP. As of now this function requires atleast version 2.1.13 of GnuPG.
key specifies the key to operate on.
userid is the user ID to be revoked from the key. The user IDmust be given verbatim because the engine does an exact and casesensitive match. Thus the uid field from the user ID object(gpgme_user_id_t) is to be used. This is a required parameter.
flags are currently not used and must be set to zero.
Note that the engine won’t allow to revoke the last valid user ID. Tochange a user ID is better to first add the new user ID, then revokethe old one, and finally publish the key.
The function returns zero on success, GPG_ERR_NOT_SUPPORTED ifthe engine does not support the command, or a bunch of other errorcodes.
SINCE: 1.7.0
The function gpgme_op_revuid_start initiates agpgme_op_revuid operation; see there for details. It mustbe completed by calling gpgme_wait on the context.See Waiting For Completion.
Gpg Create Key
SINCE: 1.8.0
The function gpgme_op_set_uid_flag is used to set flags on auser ID from the OpenPGP key given by KEY. Setting flags onuser IDs after key creation is a feature of the OpenPGP protocol andthus the protocol for the context ctx must be set to OpenPGP.
key specifies the key to operate on. This parameters is required. Generate ssh key for windows server and gitlab.
userid is the user ID of the key to be manipulated. This user IDmust be given verbatim because the engine does an exact and casesensitive match. Thus the uid field from the user ID object(gpgme_user_id_t) is to be used. This is a required parameter.
name names the flag which is to be changed. The only currentlysupported flag is:
primaryThis sets the primary key flag on the given user ID. All otherprimary key flag on other user IDs are removed. value must begiven as NULL. For technical reasons this functions bumps thecreation timestamp of all affected self-signatures up by one second.At least GnuPG version 2.1.20 is required.
The function returns zero on success, GPG_ERR_NOT_SUPPORTED ifthe engine does not support the command, or a bunch of other errorcodes.
SINCE: 1.8.0
The function gpgme_op_set_uid_flag_start initiates agpgme_op_set_uid_flag operation; see there for details. It mustbe completed by calling gpgme_wait on the context.See Waiting For Completion.
The function gpgme_op_genkey generates a new key pair in thecontext ctx. The meaning of public and secretdepends on the crypto backend.
GPG does not support public and secret, they should beNULL. GnuPG will generate a key pair and add it to thestandard key ring. The fingerprint of the generated key is availablewith gpgme_op_genkey_result.
GpgSM requires public to be a writable data object. GpgSM willgenerate a secret key (which will be stored by gpg-agent,and return a certificate request in public, which then needs tobe signed by the certification authority and imported before it can beused. GpgSM does not make the fingerprint available.
The argument parms specifies parameters for the key in an stringthat looks something like XML. The details about the format ofparms are specific to the crypto engine used by ctx. Thefirst line of the parameters must be <GnupgKeyParamsformat='internal'> and the last line must be</GnupgKeyParams>. Every line in between the first and lastlines is treated as a Header: Value pair. In particular, no XMLescaping is necessary if you need to include the characters <,>, or &.
Here is an example for GnuPG as the crypto engine (all parameters ofOpenPGP key generation are documented in the GPG manual):
Here is an example for GpgSM as the crypto engine (all parameters ofOpenPGP key generation are documented in the GPGSM manual):
Strings should be given in UTF-8 encoding. The only format supportedfor now is “internal”. The content of the GnupgKeyParmscontainer is passed verbatim to the crypto backend. Controlstatements are not allowed.
After the operation completed successfully, the result can beretrieved with gpgme_op_genkey_result.
The function returns the error code GPG_ERR_NO_ERROR if theoperation could be started successfully, GPG_ERR_INV_VALUE ifparms is not a well-formed string (e.g. does not have theexpected tag-like headers and footers), GPG_ERR_NOT_SUPPORTEDif public or secret is not valid, andGPG_ERR_GENERAL if no key was created by the backend.
The function gpgme_op_genkey_start initiates agpgme_op_genkey operation. It can be completed by callinggpgme_wait on the context. See Waiting For Completion.
The function returns the error code GPG_ERR_NO_ERROR if theoperation could be started successfully, GPG_ERR_INV_VALUE ifparms is not a valid XML string, andGPG_ERR_NOT_SUPPORTED if public or secret is notNULL.
This is a pointer to a structure used to store the result of agpgme_op_genkey operation. After successfully generating akey, you can retrieve the pointer to the result withgpgme_op_genkey_result. The structure contains the followingmembers:
unsigned int primary : 1This flag is set to 1 if a primary key was created and to 0if not.
unsigned int sub : 1This flag is set to 1 if a subkey was created and to 0 if not.
unsigned int uid : 1This flag is set to 1 if a user ID was created and to 0 if not.
char *fprThis is the fingerprint of the key that was created. If both aprimary and a subkey were generated, the fingerprint of the primarykey will be returned. If the crypto engine does not provide thefingerprint, fpr will be a null pointer.
gpgme_data_t pubkeySINCE: 1.7.0
This will eventually be used to return the public key. It iscurrently not used.
gpgme_data_t seckeySINCE: 1.7.0
Generate Gpg Key Pair Error Download
This will eventually be used to return the secret key. It iscurrently not used.
Generate Gpg Key Pair Error Key
The function gpgme_op_genkey_result returns agpgme_genkey_result_t pointer to a structure holding the result ofa gpgme_op_genkey operation. The pointer is only valid if thelast operation on the context was a gpgme_op_genkey orgpgme_op_genkey_start operation, and if this operation finishedsuccessfully. The returned pointer is only valid until the nextoperation is started on the context.
Next: Signing Keys, Previous: Manipulating Keys, Up: Key Management [Contents][Index]