Key Generation And Usage In Cryptography
Used in cryptography. 23 Key generation includes the generation of a key using the output of a r andom bit generator (RBG), 24 the derivation of a key from another key, the derivation of a key from a password, and key 25 agreement performed by two entities using an approved. Key-agreement scheme. All keys shall be. 2 EPC342-08 v8.0 Approved Guidelines on cryptographic algorithms usage and key managementfinal.
Mar 11, 2020 Public-key cryptography, or asymmetric cryptography, is a topic of broad scientific research starting back in the mid-70s, as well as the target. Uses of Cryptography. The crux of what you’ve learned so far is that cryptography is the art of writing or storing information in such a way that it’s revealed only to those who need to see it.
Runescape membership generator activation key. Key generation is the process of generating keys for cryptography. The key is used to encrypt and decrypt data whatever the data is being encrypted or decrypted.
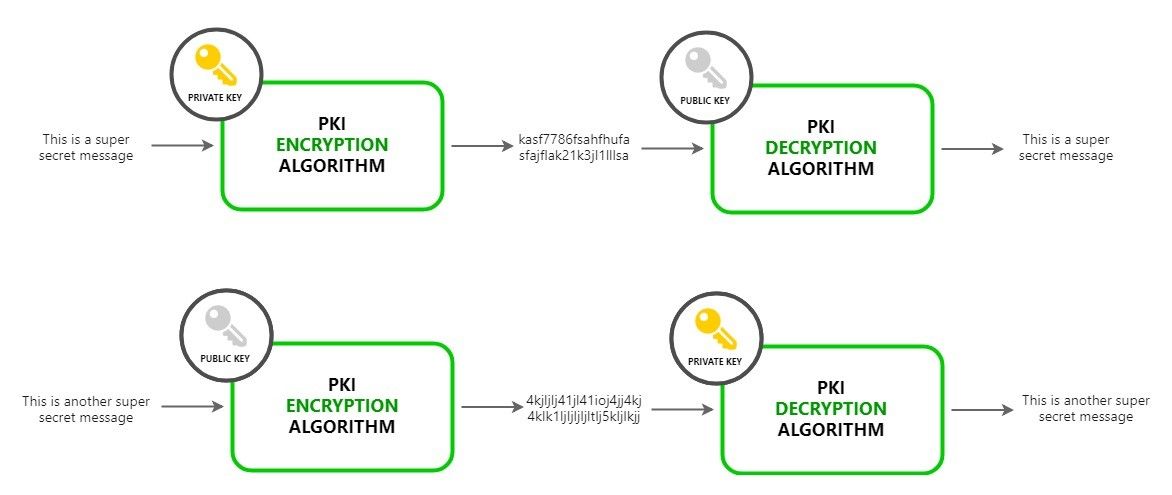
Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. The public key is made available to anyone (often by means of a digital certificate). A sender will encrypt data with the public key; only the holder of the private key can decrypt this data.
Since public-key algorithms tend to be much slower than symmetric-key algorithms, modern systems such as TLS and its predecessor SSL as well as the SSH use a combination of the two in which:
- One party receives the other's public key, and encrypts a small piece of data (either a symmetric key or some data that will be used to generate it).
- The remainder of the conversation (the remaining party) uses a (typically faster) symmetric-key algorithm for encryption.
The simplest method to read encrypted data is a brute force attack–simply attempting every number, up to the maximum length of the key. Therefore, it is important to use a sufficiently long key length; longer keys take exponentially longer time to attack, making a brute force attack invisible and impractical.
Currently, commonly used key lengths are:
- 128-bits for symmetric key algorithms.
- 1024-bits for public-key algorithms.
Key generation algorithms[changechange source]
In computer cryptography keys are integers. In some cases keys are randomly generated using a random number generator (RNG) or pseudorandom number generator (PRNG), the latter being a computeralgorithm that produces data which appears random under analysis. Some types the PRNGs algorithms utilize system entropy to generate a seed data, such seeds produce better results, since this makes the initial conditions of the PRNG much more difficult for an attacker to guess.
In other situations, the key is created using a passphrase and a key generation algorithm, using a cryptographic hash function such as SHA-1.

Related pages[changechange source]
- Distributed key generation: For some protocols no party should be in the sole possession of the secret key. Rather, during distributed key generation every party obtains a share of the key. A threshold of the participating parties need to work together in order to achieve a cryptographic task, such as decrypting a message.
References[changechange source]
Public Key Cryptography Explained